Introduction to Cybersecurity in Process Plant Architecture
Process plants, such as chemical manufacturing facilities, oil refineries, power generation stations, and water treatment systems, rely on complex architectures involving industrial control systems (ICS), supervisory control and data acquisition (SCADA) systems, programmable logic controllers (PLCs), and other operational technology (OT) components. These systems manage physical processes like fluid flow, temperature control, and chemical reactions, often in real-time. However, the increasing convergence of OT with information technology (IT) networks—driven by digital transformation, remote monitoring, and cloud integration—has amplified cybersecurity risks.
When we say OT i.e. Operational Technology, we are mainly referring to Industrial Control Systems(ICS).
Industrial Control Systems (ICS) are technologies and systems oriented toward physical equipment/Machinery, that deals with the actual operation of plants and equipment, incorporating devices that ensure system integrity and meet technical constraints, and functioning as event-driven, often real-time software applications or devices with embedded software.
The Specialized devices that we are talking about here, use Industrial standards and implement specialized technologies for Sensing and Data propagation for interpretation.
These specialized systems are pervasive across infrastructure, required to meet numerous, often conflicting requirements for safety, performance, security, reliability, and operations.
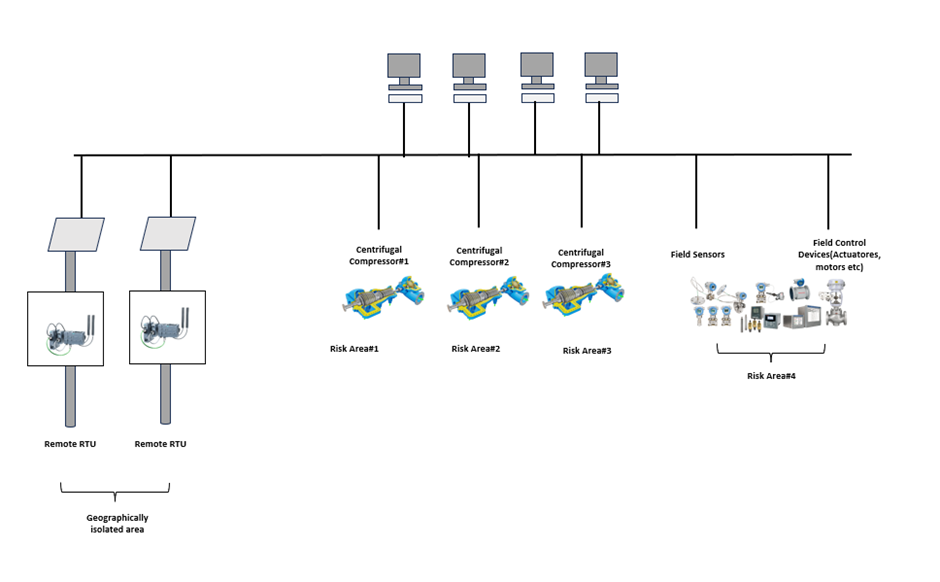
ICSs spans thoughout the Control Architecture as specialized systems with Sensing Devices, Control Panels(Located in the Field or Located in Control Room/Rack(Equipment) Room).
An ICS via a broad point of View can be seen based on a certain Geographical area, Risk Area within that Geographical area, Process related(Licensor defined/supplied), etc.
The term Industrial Control Systems (ICS), in its widest scope, covers a variety of systems, including:
Transportation Systems, enabling advanced traffic and transport management.
An explanatory diagram showing a typical Architecture (Level 0/1) of an ICS is shown below.
Information Technology (IT) on the other hand refers to the use of computers, networks, software, and related technologies to manage, process, store, and transmit data, primarily for business and administrative purposes. In the context of the provided text about Industrial Control Systems (ICS) and Operational Technology (OT), IT represents the enterprise-level systems that contrast with OT’s focus on controlling physical processes.
Industrial Control Systems (ICS) differ from traditional IT systems, using specialized software, hardware, and protocols tailored for physical process control. ICS often integrate with organizational IT systems to enable connectivity, efficiency, and remote access, with their “front end” using commercial IT components, introducing IT-like vulnerabilities. As ICS components became digital and IP-enabled, their connections to business networks exposed organizations to exploits, especially due to unclear boundaries (e.g., an EMCS meter on a SCADA or BAS system).
Table 1: IT vs. OT Systems Comparison
| Aspect | Information Technology | Operational Technology |
|---|---|---|
| Purpose | Gathering of Information via Process data updates/Transactions | Control/monitor Process Plant variables |
| Architecture | Generic enterprise-wide infrastructure, applications | Custom, event-driven, real-time, embedded systems |
| Interfaces | GUI, web browser, keyboard, terminal | Sensors, actuators, electromechanical, coded displays, hand-held devices |
| Ownership | CIO, IT teams | Engineers, technicians, operators, managers |
| Connectivity | IP-based corporate networks | Hardwired, twisted pair, or IP-based control networks |
| Role | Supports people | Controls machines |
ICS often have long lifespans (25+ years in some cases) and slower technology refresh cycles than IT, creating challenges: outdated systems may lack patches or upgrades, and modern security scans (e.g., IDS, HBSS) can disrupt operations, potentially causing shutdowns. Security updates for ICS require thorough impact analysis, delaying deployment and necessitating flexible compliance approaches.
Importance of Cybersecurity in Process Plants
Process plants operate in high-stakes environments where cyber incidents can cascade into real-world impacts. Risks include:
- Infrastructure Compromise: Attackers targeting critical assets like PLCs or safety-instrumented systems to alter processes, leading to explosions, leaks, or shutdowns.
- Data Theft or Alteration: Stealing intellectual property (e.g., proprietary formulas) or manipulating sensor data to hide malfunctions.
- Supply Chain Vulnerabilities: Third-party vendors or connected devices introducing malware, as modern operations rely on interdependent ecosystems.
- Human Factors: Phishing, insider threats, or weak policies enabling unauthorized access.
- Evolving Threats: Nation-states, organized crime, terrorists, or activists using sophisticated methods, with ICS-targeted events rising 210% over recent years according to U.S. Department of Homeland Security reports.
Without robust cybersecurity, plants face regulatory non-compliance, financial losses (e.g., Merck’s $1.3 billion from 2017 ransomware), reputational damage, and legal liabilities. Conversely, secure architectures enable benefits like predictive maintenance, data analytics, and optimized production through safe cloud connectivity.
Cybersecurity in process plant architecture focuses on designing resilient systems that prioritize availability, integrity, and confidentiality while minimizing vulnerabilities. Essentials include layered defenses (defense-in-depth), network segmentation, risk management, and adherence to standards. Unlike traditional IT security, OT cybersecurity must avoid measures that could cause unplanned downtime, as process interruptions can have immediate safety and financial consequences. Effective implementation requires collaboration between plant engineers, IT teams, and leadership, treating cybersecurity as an enterprise-wide ecosystem challenge rather than a purely technical fix.
Key Architectural Essentials
Process plant architecture should follow a structured model to isolate and protect components. The Purdue Enterprise Reference Architecture (PERA), or Purdue Model, is a foundational framework dividing systems into hierarchical levels for security zoning:
| Level | Description | Security Focus |
|---|---|---|
| Level 0: Process | Physical sensors, actuators, and valves controlling real-world operations. | Protect against tampering; ensure integrity of data inputs/outputs. |
| Level 1: Basic Control | PLCs and controllers executing logic for process automation. | Harden devices; restrict direct external access. |
| Level 2: Supervisory Control | HMIs, SCADA systems for monitoring and control. | Implement access controls; monitor for anomalies. |
| Level 3: Operations Management | Historians, production planning tools. | Segment from higher levels; enable secure data flow. |
| Level 4: Enterprise/IT | Business systems, ERP integration. | Use firewalls to separate from OT; manage remote access. |
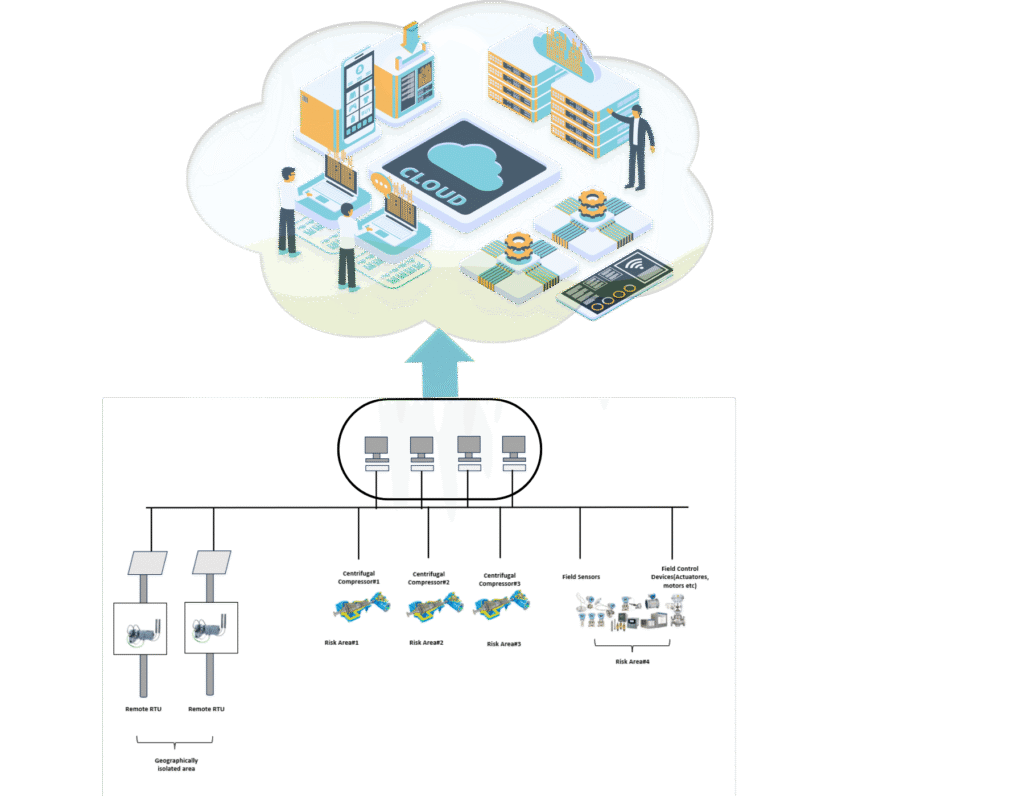
| Level 5: Cloud/Internet | External services for analytics or remote monitoring. | Employ DMZs and encrypted conduits for safe connectivity. |
This model supports zoning (grouping assets by function/risk) and conduits (controlled pathways between zones), limiting threat propagation. Defense-in-depth adds multiple safeguards, such as firewalls, intrusion detection, and diversity in protections to avoid single points of failure.

Additional essentials:
- Secure Endpoints and Controllers: Harden workstations, HMIs, and PLCs by patching vulnerabilities, disabling unnecessary services, and using whitelisting to block unauthorized software. Many legacy systems (e.g., on Windows XP) require careful upgrades.
- Network Design: Use VLANs for logical separation, firewalls for traffic control, and DMZs for external interfaces. Avoid air-gapping, as it’s ineffective against modern threats like USB-based malware.
- Integration with Functional Safety: Ensure cybersecurity supports safety systems (e.g., per IEC 61511), as cyber attacks can undermine safety integrity levels.
Standards and Frameworks
The IEC 62443 series is the primary standard for industrial cybersecurity, providing a risk-based approach applicable to process plants. It organizes into four groups: General, Policies and Procedures, System, and Component, covering terminology, security programs, technical requirements, and product lifecycles.
Key elements:
- Foundational Requirements (FRs): Seven core areas like identification/control, use control, system integrity, data confidentiality, restricted data flow, timely response, and resource availability.
- Security Levels (SL 0-4): Scale from no protection (SL 0) to defense against highly motivated, sophisticated attackers (SL 4). Plants assess target (SL-T), capability (SL-C), and achieved (SL-A) levels for zones and components.
- Cybersecurity Management System (CSMS): Lifecycle processes for risk assessment, patch management, and service provider requirements (e.g., IEC 62443-2-1, -2-4).
- System and Component Requirements: Risk partitioning (IEC 62443-3-2), technical controls (IEC 62443-3-3), secure development (IEC 62443-4-1), and component hardening (IEC 62443-4-2).
Other frameworks include NIST Cybersecurity Framework (for risk management), CIS Controls (basic hygiene), and NERC CIP (for utilities). Compliance often involves certification for products, sites, or personnel.
Best Practices and Tips
Implement a layered strategy focusing on people, processes, and technology:
- Risk Assessment: Inventory assets, map data flows, evaluate threats/vulnerabilities, and prioritize based on impact. Conduct regular audits, penetration tests, and use frameworks like RAGAGEP (Recognized and Generally Accepted Good Engineering Practices).
- System Hardening: Update patches during planned outages, enforce least privilege, change defaults, and use multi-factor authentication (MFA). Apply to all levels, including legacy equipment.
- Network Segmentation: Isolate zones with firewalls and VLANs; monitor conduits for unauthorized traffic.
- Access Controls: Role-based access, account management, and auditing to prevent insider/external breaches.
- Monitoring and Detection: Use IDS, SIEM for anomaly detection, log aggregation, and threat hunting. Integrate with backups for quick recovery.
- Incident Response: Develop plans with teams, playbooks, and simulations. Include escalation, forensics, and stakeholder communication.
- Policies and Training: Establish policies for access, patches, changes, and audits. Train staff on phishing and behaviors; foster IT-OT collaboration.
- Supply Chain and Vendor Management: Vet third parties, ensure secure integrations, and address IIoT risks.
Ongoing vigilance, expert partnerships, and integration with business risk management ensure long-term resilience in process plant architectures.
Elaboration on Cybersecurity in Process Plant Architecture
Building on the foundational overview of cybersecurity in process plants, this section provides a deeper dive into the Purdue Enterprise Reference Architecture (PERA), also known as the Purdue Model. This model structures industrial control systems (ICS) into hierarchical levels, emphasizing segmentation to enhance security. Each level includes specific systems, interfaces to adjacent levels, and associated risks. The model divides into Operational Technology (OT) zones (Levels 0-3), which focus on real-time physical processes, and Information Technology (IT) zones (Levels 4-5), which handle business and enterprise functions. A key area of vulnerability is the IT-OT interface, often at Level 3.5 (a demilitarized zone or DMZ), where convergence occurs to enable data sharing while introducing risks.
The Purdue Model promotes defense-in-depth by using zones (logical groupings of assets) and conduits (secure communication pathways between zones). Interfaces are typically managed through firewalls, data diodes (one-way data flow devices), or proxies to control traffic. Risks at each level stem from legacy equipment, human error, supply chain weaknesses, and evolving threats like ransomware or nation-state attacks. Below, I elaborate level by level, including systems, interfaces, and risks.
Detailed Systems, Interfaces, and Risks by Purdue Model Level
The following table expands on the Purdue Model levels, detailing typical systems, key interfaces (including protocols and security controls), and primary risks. This hierarchical structure ensures that lower levels (closer to physical processes) are isolated from higher ones, reducing the blast radius of breaches.
| Level | Systems and Components | Interfaces and Protocols | Key Risks and Mitigation Strategies |
|---|---|---|---|
| Level 0: Process (Physical Process) | Includes field devices such as sensors (e.g., pressure, temperature), actuators (e.g., valves, pumps), meters, and transmitters that directly interact with the physical environment. These are often analog or digital I/O devices in harsh industrial settings. | Interfaces primarily to Level 1 via hardwired connections or fieldbus protocols like HART, Foundation Fieldbus, or PROFIBUS. Minimal to no direct external interfaces; data flow is unidirectional upward. Security controls: Physical access restrictions and tamper-evident seals. | Risks: Physical tampering or sensor spoofing (e.g., false readings leading to process instability). Legacy devices lack encryption, making them vulnerable to eavesdropping. Mitigation: Implement input validation, physical security (e.g., locked cabinets), and regular calibration checks. High impact if compromised, as it directly affects safety (e.g., overpressurization causing explosions). |
| Level 1: Basic Control (Direct Control) | Comprises controllers like Programmable Logic Controllers (PLCs), Remote Terminal Units (RTUs), Distributed Control Systems (DCS), and safety-instrumented systems (SIS). These execute real-time logic for process control, often using ladder logic or function blocks. | Interfaces downward to Level 0 via I/O modules and upward to Level 2 via industrial Ethernet (e.g., Modbus TCP, EtherNet/IP) or serial protocols. Conduits include switches with VLANs for segmentation. Security: Whitelisting and protocol filtering to prevent unauthorized commands. | Risks: Malware injection (e.g., Stuxnet altering PLC code), denial-of-service (DoS) disrupting timing-critical operations, or unpatched vulnerabilities in proprietary firmware. Insider threats via USB ports. Mitigation: Firmware integrity checks, network isolation, and air-gapping where feasible; avoid internet exposure. Compromise can lead to immediate physical damage or shutdowns. |
| Level 2: Supervisory Control (Area Supervision) | Features Human-Machine Interfaces (HMIs), SCADA servers, engineering workstations, and alarm management systems for monitoring and operator intervention. Data aggregation occurs here for visualization. | Interfaces downward to Level 1 via OPC (OLE for Process Control) or proprietary protocols, and upward to Level 3 via Ethernet with firewalls. Often includes wireless access points for mobile operators. Security: Role-based access control (RBAC) and session timeouts. | Risks: Operator errors from phishing on HMIs, screen scraping for data exfiltration, or buffer overflows in SCADA software. Flat networks allow lateral movement from compromised workstations. Mitigation: Multi-factor authentication (MFA), anomaly detection tools, and segregated operator networks. Breaches here can enable attackers to manipulate views, hiding real issues like leaks. |
| Level 3: Operations Management (Site Operations) | Involves Manufacturing Execution Systems (MES), data historians (e.g., OSIsoft PI), batch management, asset management, and laboratory information systems. Focuses on production scheduling and performance analytics. | Interfaces downward to Level 2 via data historians or APIs, and upward to Level 4 via DMZ conduits (e.g., secure FTP or web services). Protocols include SQL for databases or MQTT for IIoT integration. Security: Encryption (e.g., TLS) and data diodes for one-way flow. | Risks: Data manipulation in historians leading to faulty decision-making, or SQL injection attacks exposing operational data. Increased IIoT devices amplify supply chain risks. Mitigation: Regular backups, access logging, and vulnerability scanning during maintenance windows. This level bridges OT and IT, heightening exposure to hybrid threats. |
| Level 3.5: Demilitarized Zone (DMZ – IT/OT Convergence Layer) | Not always explicitly in the original model but added in extensions; includes proxy servers, firewalls, intrusion detection systems (IDS), and remote access gateways for secure data exchange without direct IT-OT connectivity. | Acts as a buffer: Interfaces to Level 3 via mirrored databases or replication servers, and to Level 4 via controlled ports (e.g., only HTTP/HTTPS). No direct routing between IT and OT; uses jump servers for maintenance. Security: Network Address Translation (NAT) and deep packet inspection. | Risks: Misconfigured firewalls allowing bidirectional traffic, or compromised proxies enabling pivoting attacks. Vendor remote access tools (e.g., VPNs) as entry points. Mitigation: Strict allow-listing, zero-trust principles, and continuous monitoring. This layer is critical for containing IT threats from propagating to OT. |
| Level 4: Business Logistics (Site Business Planning) | Encompasses Enterprise Resource Planning (ERP) systems, supply chain management, scheduling tools, and email servers integrated with business processes. | Interfaces downward to Level 3.5 via DMZ for data pulls (e.g., production metrics), and upward to Level 5 via corporate networks. Protocols: Standard IT like HTTP, SMTP. Security: Firewalls and VPNs for remote access. | Risks: Ransomware spreading from email attachments to OT via weak segmentation, or API vulnerabilities in ERP integrations exposing sensitive data. Cloud syncing amplifies data leakage. Mitigation: Endpoint detection and response (EDR), patch management, and user training. High financial impact from downtime or IP theft. |
| Level 5: Enterprise (Corporate Network) | Includes cloud services, external web applications, CRM systems, and connections to partners or the internet for analytics, remote monitoring, or e-commerce. | Interfaces downward to Level 4 via WAN or internet gateways, often with cloud APIs (e.g., AWS IoT). No direct OT access. Security: Web application firewalls (WAF) and identity access management (IAM). | Risks: Phishing or supply chain attacks (e.g., SolarWinds-style) introducing malware that traverses downward. External threats like DDoS targeting cloud links. Mitigation: Segmentation, encryption, and third-party audits. Global connectivity increases espionage risks from nation-states. |
Interfaces in Process Plant Architecture
Interfaces between levels are designed as controlled conduits to enforce security policies. Common types include:
- Physical/Protocol Interfaces: Hardwired at lower levels (e.g., 4-20mA signals from Level 0 to 1) transitioning to Ethernet-based at higher levels.
- Security Controls: Firewalls inspect traffic (e.g., allowing only specific ports like 502 for Modbus), data diodes ensure unidirectional flow (OT to IT), and IDS monitor for anomalies.
- Modern Extensions: With Industry 4.0, interfaces incorporate IIoT gateways using protocols like OPC UA for secure, standardized data exchange. However, these add complexity, requiring certificate management and encryption.
Poorly managed interfaces lead to “flat” networks, where a breach at one level enables unrestricted access to others, violating the model’s segmentation principle.
Risks with IT-OT Interface and Convergence
The IT-OT interface, primarily at Levels 3-4 via the DMZ, represents the convergence point where digital transformation benefits (e.g., real-time analytics, predictive maintenance) meet heightened risks. Historically, OT was air-gapped, but convergence—driven by cloud integration, remote access, and IIoT—has eroded this isolation, expanding the attack surface.
Key risks include:
- Increased Attack Vectors: IT threats like phishing or unpatched Windows systems in Level 4 can propagate to OT via misconfigured DMZs, allowing lateral movement (e.g., ransomware locking PLCs, as in Colonial Pipeline).
- Cultural and Priority Clashes: IT prioritizes confidentiality and updates, while OT emphasizes availability—leading to delayed patching in OT, creating exploitable vulnerabilities.
- Supply Chain and Third-Party Risks: Vendors accessing OT through IT interfaces (e.g., remote diagnostics) can introduce malware; IIoT devices often have weak defaults.
- Data Flow Issues: Bidirectional interfaces risk command injection from IT to OT, altering processes (e.g., TRITON targeting safety systems).
- Regulatory and Compliance Gaps: Non-compliance with IEC 62443 or NIST can result in fines; convergence complicates audits across silos.
- Evolving Threats: Sophisticated attacks exploit convergence, such as zero-days in shared protocols or AI-driven reconnaissance.
Mitigations emphasize zero-trust architecture: Verify all access, segment rigorously, monitor continuously (e.g., with SIEM integrating IT/OT logs), and conduct joint IT-OT tabletop exercises. Standards like IEC 62443-3-3 guide secure interfaces, requiring risk assessments for each conduit. Ultimately, treating IT-OT convergence as a strategic opportunity rather than a vulnerability—through unified governance—enhances resilience in process plants.